I Just Want Authentication To Work
Authentication is the process of verifying the identity of a user or entity. It is a fundamental security measure that is used in a wide variety of...
November 17, 2023
Categories
Authentication is the process of verifying the identity of a user or entity. It is a fundamental security measure that is used in a wide variety of...
November 17, 2023
Reduce the overhead associated with customer authentication and authorization when creating a .NET web application using FusionAuth templates.
October 26, 2023
For many applications, a user is forced to register for application access. You want to know who the user is so you can provide them with individualized...
October 2, 2023
So, you have just set up FusionAuth and are excited to take your new customer identity and access management platform out for a spin. You spend some time...
September 1, 2023
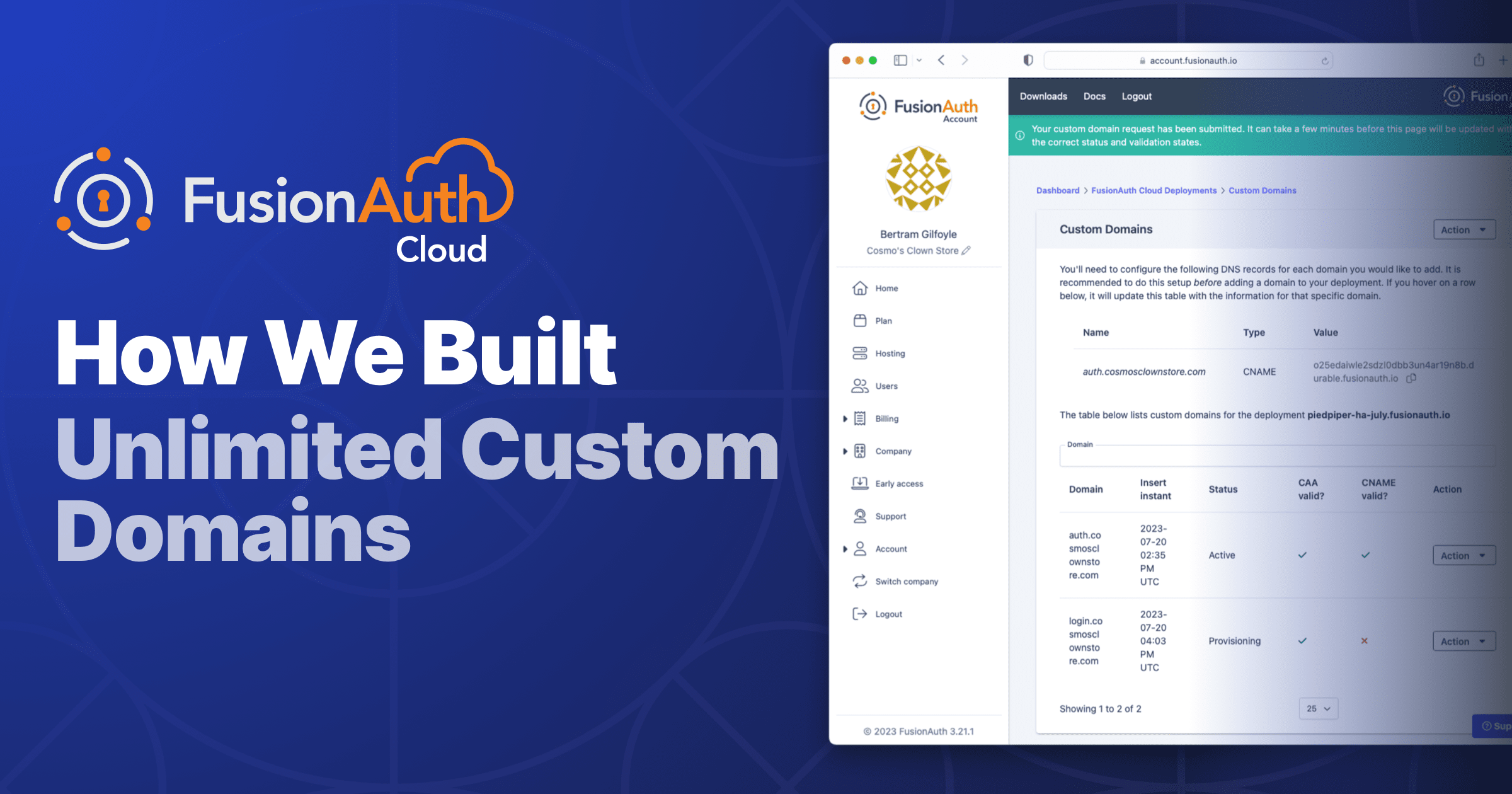
In the world of cloud services, offering 'unlimited' often feels like a stretch. But we've done just that. We recently unveiled support for unlimited custom...
August 24, 2023

Happy world password day! This is a great day to change your passwords on important accounts such as banking, email or social media systems.
May 4, 2023
At the end of the OAuth Authorization Code grant, after a user presents their credentials at login, a code is returned which can be exchanged for one or more...
January 19, 2023
Get updates on techniques, technical guides, and the latest product innovations coming from FusionAuth.
Just dev stuff. No junk.