@joshua To add on to what @adil was saying, we want to be able to block users signing up for the app unless they have an invite token. The invite token may not have an email address associated with it which matches the login they create (ex. if create a user/register a user with an appleid, the email for the account will be the proxy email apple gives out, not their actual email).
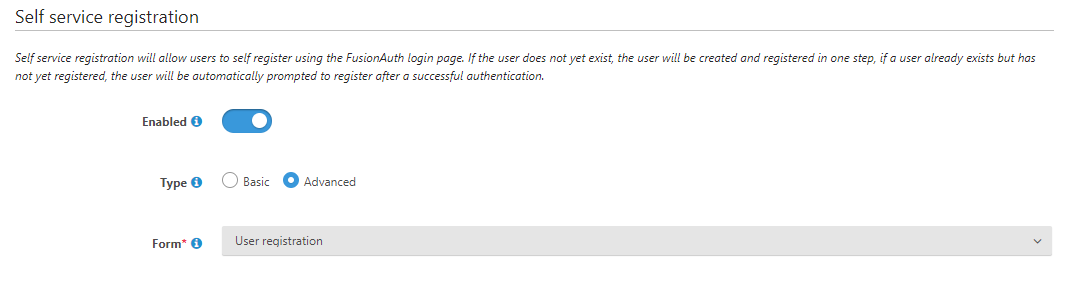
Currently, we are set up so that when a user logs in with an Identity Provider account (ex. Google, Apple, etc) it will autocreate a FusionAuth user account and register that user with our application.
Our initial screen gives the option to enter an invite code or log in, kicking off two flows:
Invite Code Flow
We send the invite code as an additional parameter in the query string to the oauth login page. We can get the parameter and pass it along to the other pages in the login flow by modifying the theme templates. However, if they choose to create an account with one of the IdPs, we lose the identity token when it reverts to a flow controlled by the template (actually, in the current version it doesn't seem to hit the template at all).
What we'd like to do is include the invite token in the webhook call back to our main server either when the user account is created or when the registration for that new user account is performed. This would allow us to expire the invite token and associate the FusionAuth user with the invite. The only place available to put custom data seems to be the data section of the user object itself. We can't figure out how to include additional information in the redirect URL, however (we can't populate state, since that's already used for what seems like a CSRF token).
The broader question here is how can we associate our own state with the account creation/registration process such that we're able to pass that state back to either our server (via webhook) or to the client hosting the page (the final redirect fusionauth does back to the main application)?
Login Flow
If the user enters the login page without the invite token, we'd like to prevent logging in with an IdP account from autocreating a user account, registering it with the application, and logging the user in. Alternatively, if we're not able to block account creation under those circumstances, we'd like to be able to determine that the account was created without an invite token (we could do some more complicated logic to remove the account and prevent the user from actually logging in).