
Product
Platform
Platform
Platform
Developers
Quickstarts
Resources
Explore
Pricing
Download
get a demoLogin

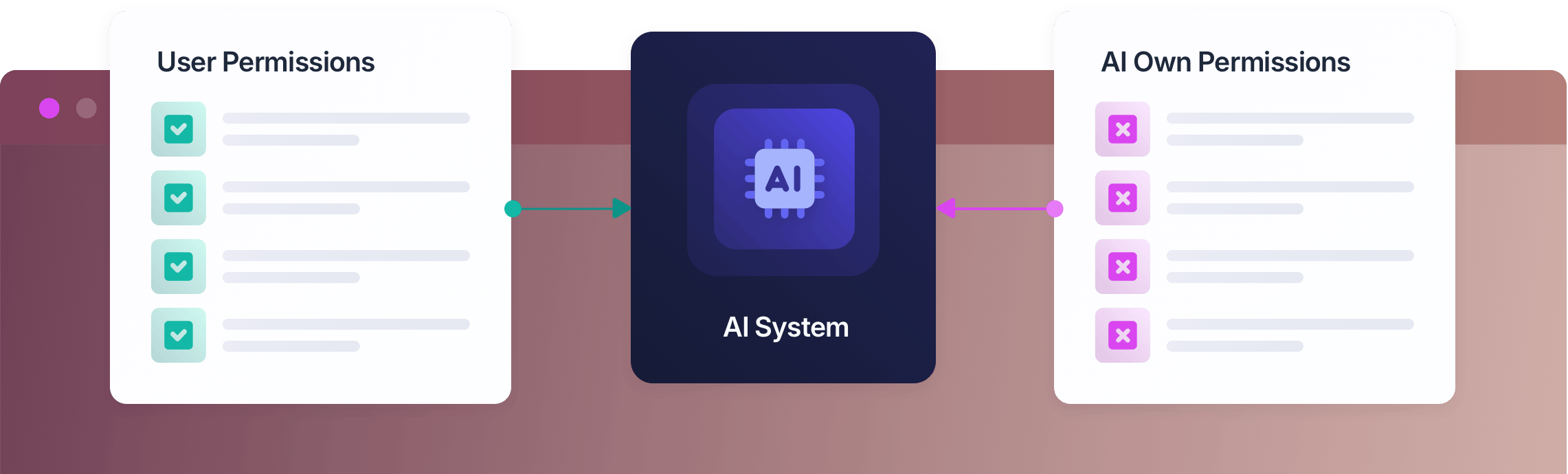
AI systems should inherit permissions from authenticated users and services, not invent their own.

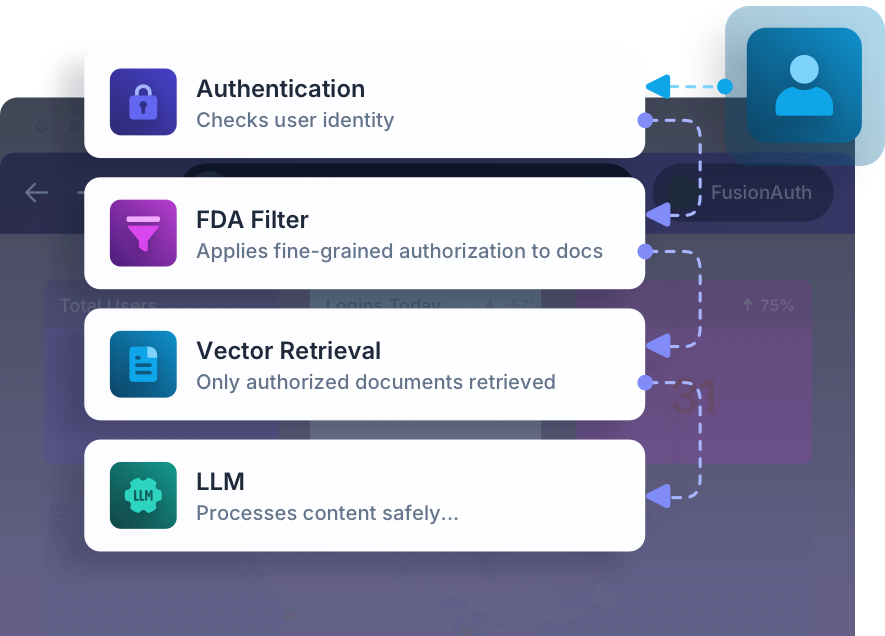
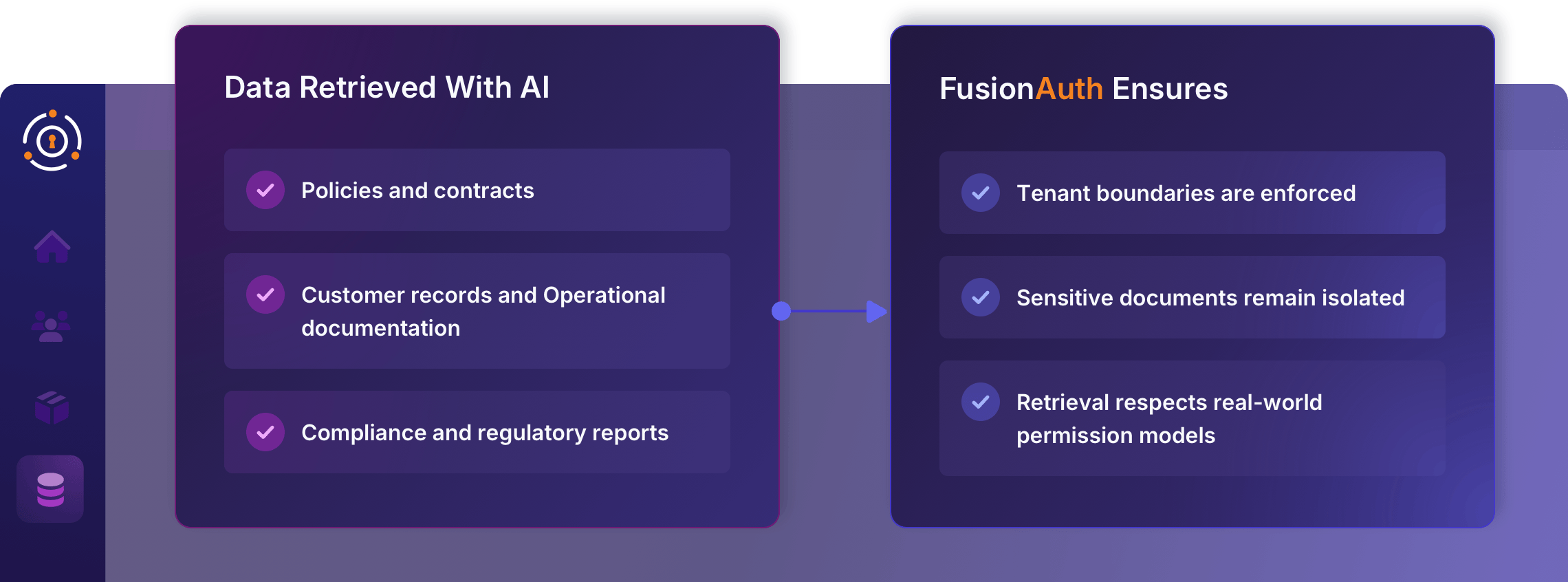
AI no longer assists at the edges — it retrieves sensitive data, calls production APIs, and executes workflows. That requires more than intelligence. It requires authority. FusionAuth Ensures:
AI can expand what your software can do. Identity ensures it operates within defined limits.
As AI interacts with core systems, access control becomes the deciding factor between growth and exposure.
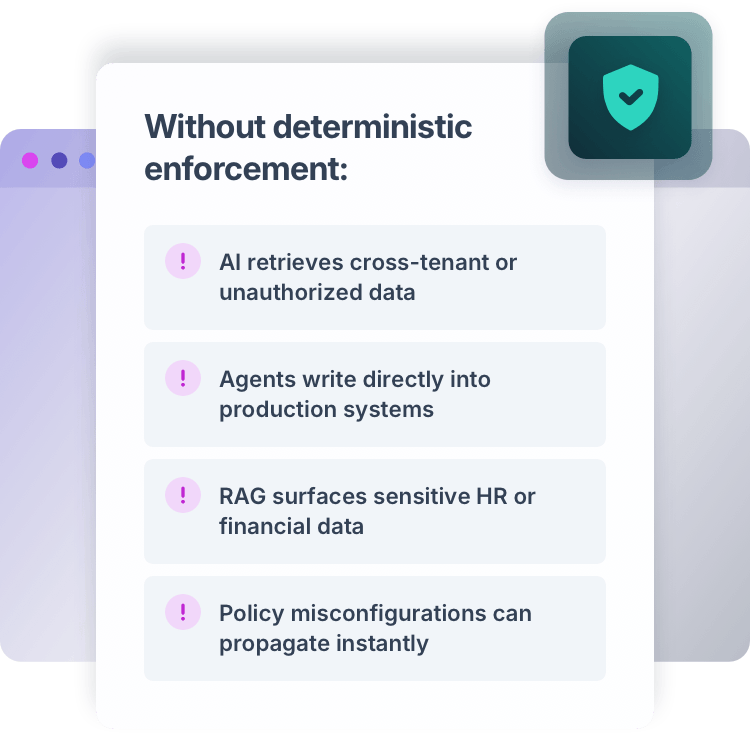
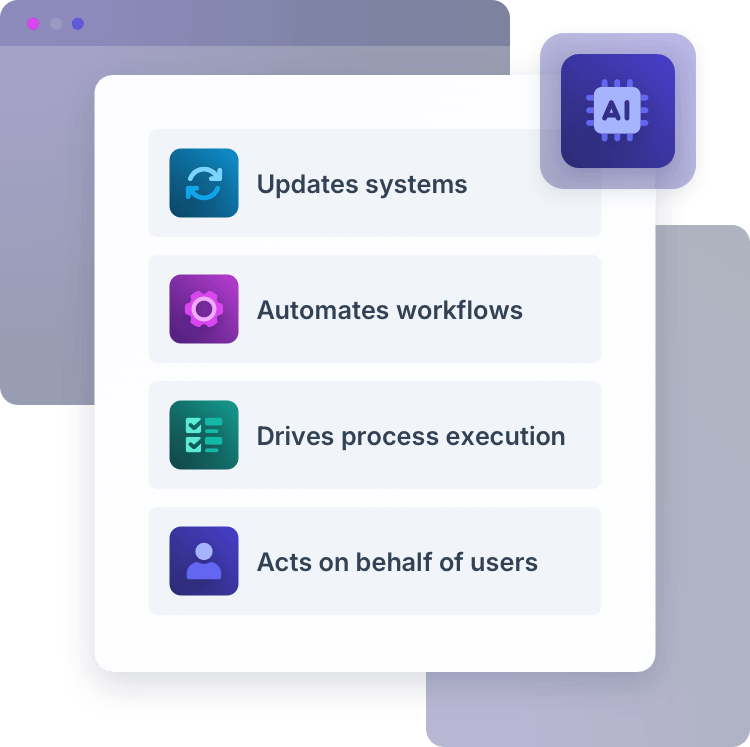
AI is now embedded into applications powering knowledge retrieval, automating workflows, and acting on behalf of users. But AI systems are probabilistic and identity systems must remain deterministic.
A single access mistake can become systemic; without clear identity boundaries, AI turns from an asset into a risk.
Organizations that succeed with AI will be those that anchor it to identity first.
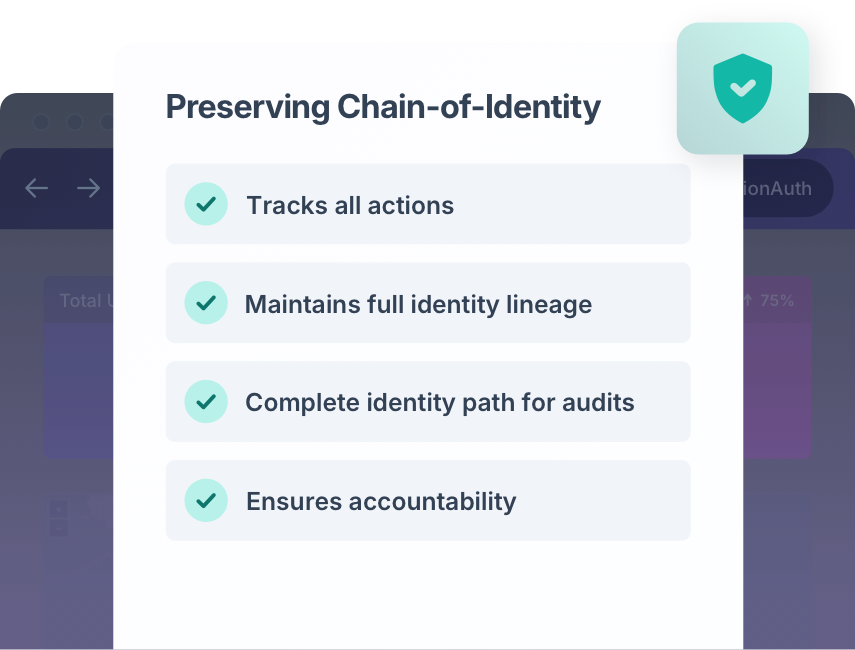
FusionAuth ensures AI systems operate within governed identity boundaries, preserving compliance, auditability, and control as automation scales.
FusionAuth supports secure AI adoption across internal and product-facing environments.
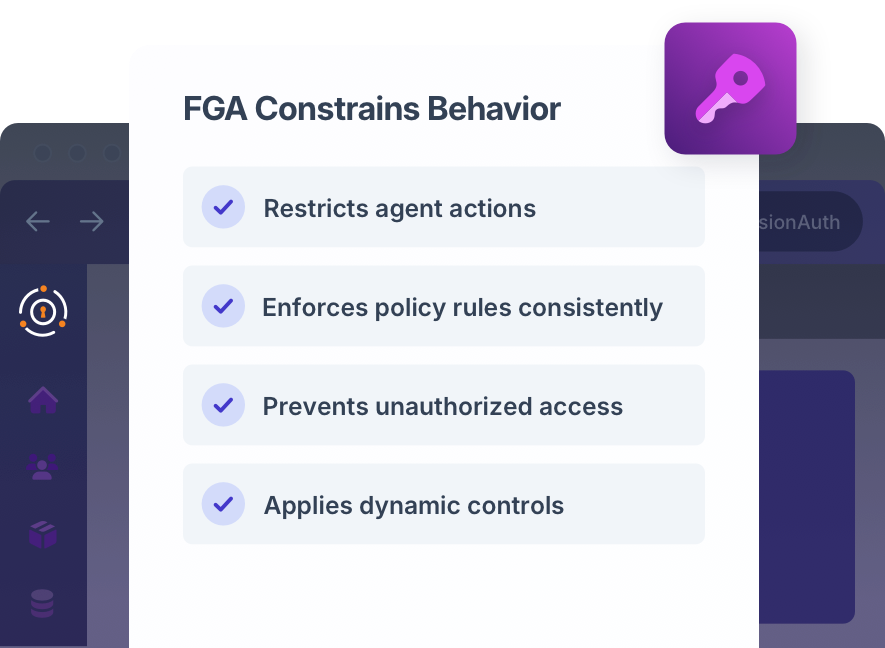
AI updates systems, triggers action, and executes business logic on behalf of users. And FusionAuth ensures that:
Automation never exceeds user authority
Production systems remain protected
Every action is attributable
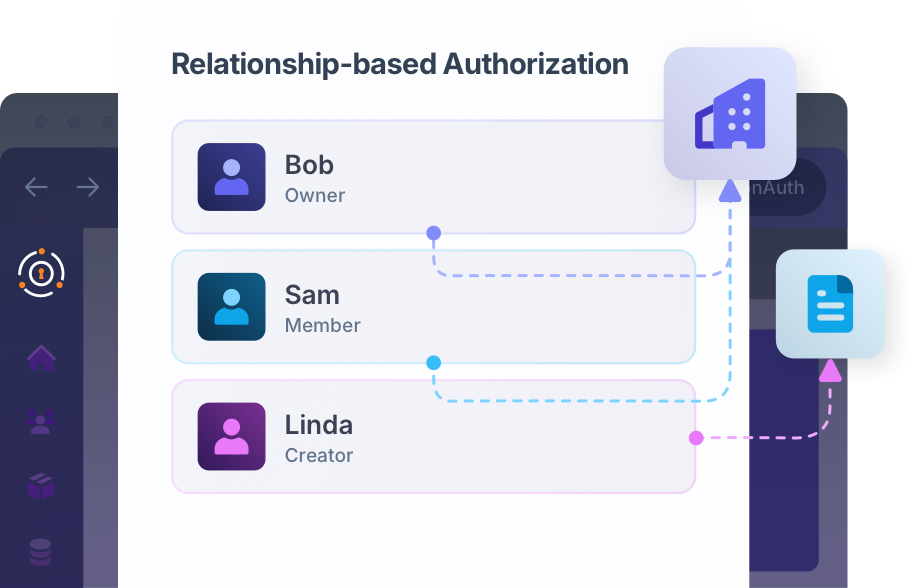
Internal employees or end users in a multi-tenant SaaS product use AI to retrieve data.

AI agents coordinate approvals, onboarding, or cross-system orchestration.